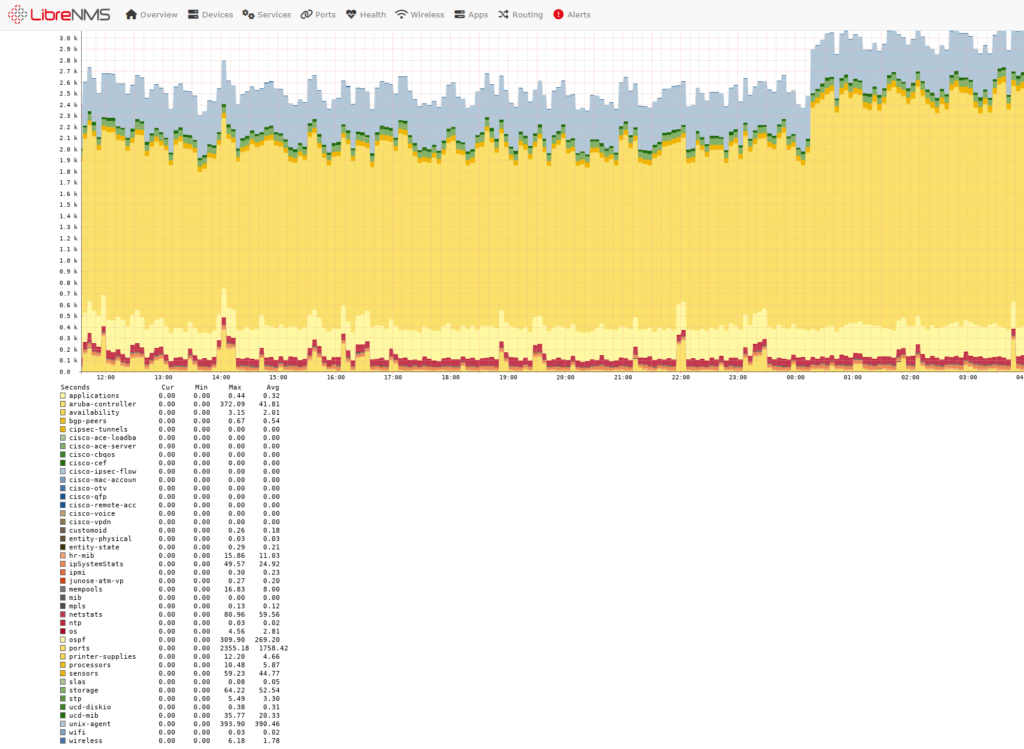
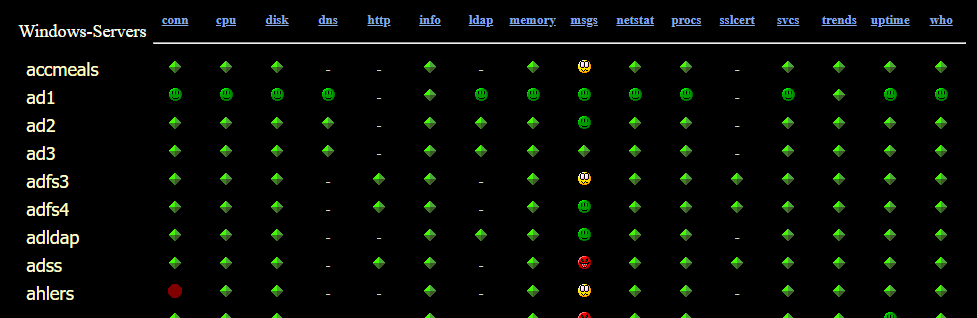
Mass Delete Devices from LibreNMS with Operating System: Generic Device
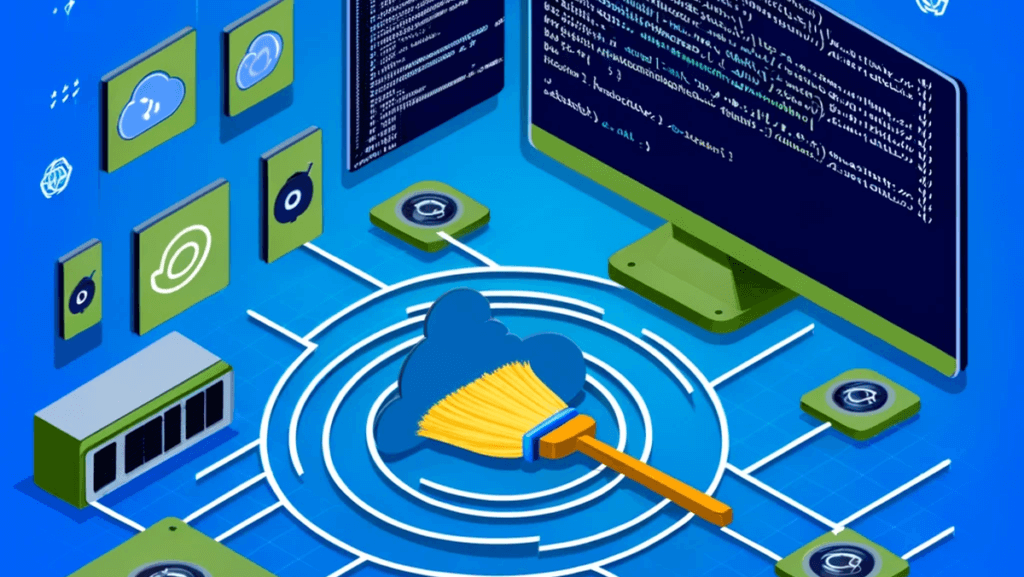
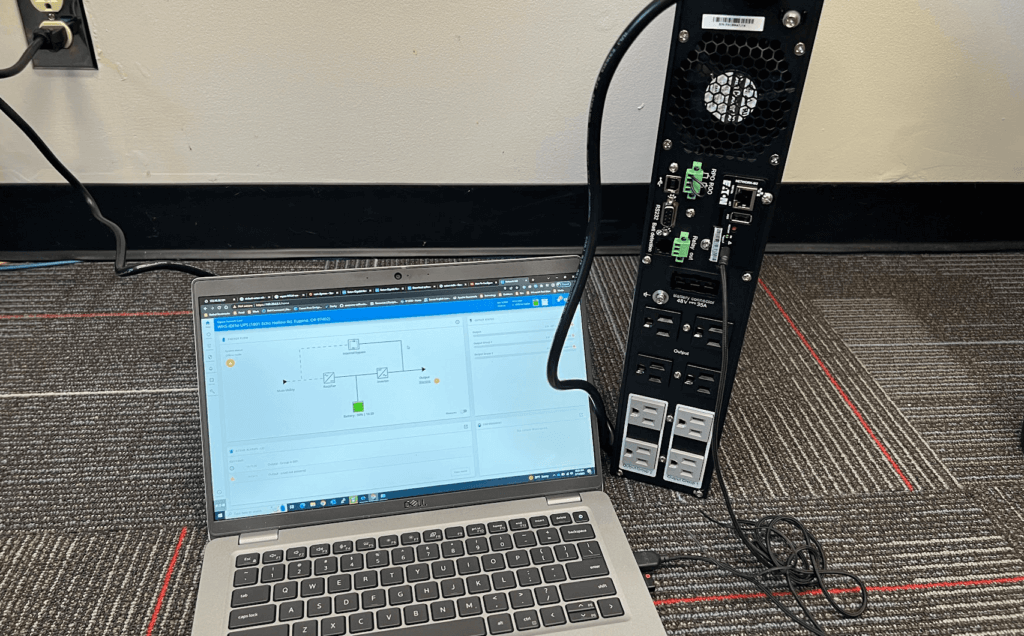
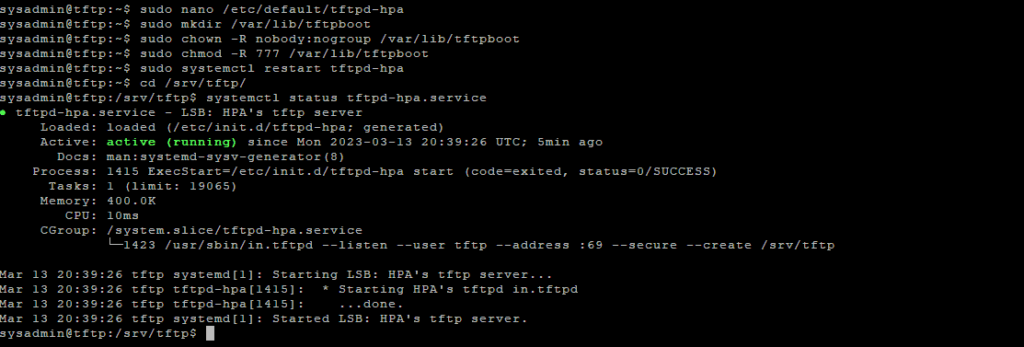
Recently, we embarked on expanding our network monitoring capabilities by adding a new subnets to our LibreNMS auto-discovery configuration. The goal was straightforward: to ensure comprehensive visibility across our network. However, the outcome was anything but expected. Instead of the anticipated additions, we found ourselves sifting through an influx of devices – a total that […]
Mass Delete Devices from LibreNMS with Operating System: Generic Device Read More »